Securing Your Network Perimeter
By A Mystery Man Writer
Description
Securing your network perimeter is essential to protect critical internal data from external threats. What does network perimeter means and how it works?
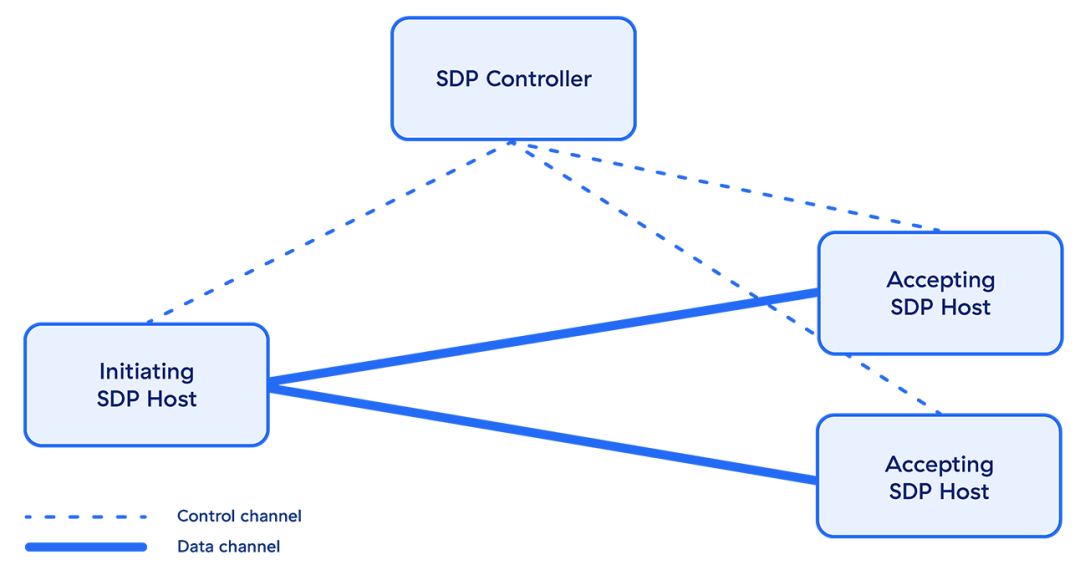
What is a Software Defined Perimeter (SDP)?

How to Test and Improve Your Network Security

Perimeter Network - an overview
PPT - SECURING YOUR NETWORK PERIMETER PowerPoint Presentation

The Security Posture Checklist: Tips for Strengthening Your Digital Defenses

Perimeter Network - an overview

A New Way to Secure Your IT Infrastructure, Blog
7 Layers of Data Security: Perimeter
Defining Your IT Network Security Perimeter

Facing Cybersecurity Risk? Here are 6 Ways to Minimize - Millers Insurance Group

dig8ital Cyber Security Services & Consulting Germany UK Australia Global

How to Build Secure Network Perimeter with Zero Trust?

How to Design a Secure Network Topology
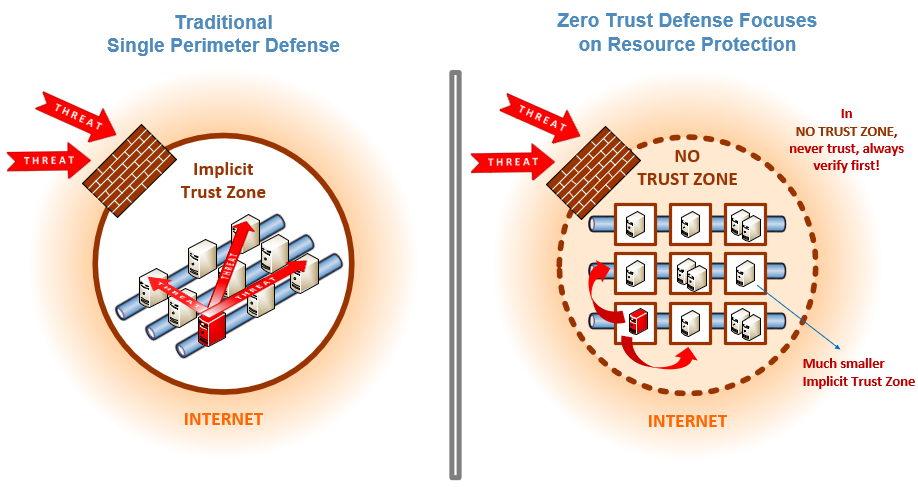
Zero Trust Cybersecurity: 'Never Trust, Always Verify
IT security: 5 things you can do to secure your network perimeter
from
per adult (price varies by group size)